DecCom
DecCom is an open-source framework for the construction of modular protocol stacks. It focuses on ease of usage, throughput, and security. Its modular nature means that you can reuse/modify parts of your application without needing to rewrite the entire codebase.
We currently support the following programming languages:
- Python - https://pypi.org/project/deccom/
THIS TOOL IS STILL IN DEVELOPMENT! ALL BINDINGS ARE SUBJECT TO CHANGE. WE PRESENT THIS ARTICLE FOR ANYONE INTERESTING IN TRYING DECCOM OUT AND PROVIDING FEEDBACK
Why DecCom?
Many popular frameworks for distributed applications are often overly complex, poorly maintained, or straight up not working. IPv8 has an incredibly rigid structure and poor throughput. LibP2P has a tidiously slow developmental cycle and for many languages the repositories are no longer maintained. It is incredibly difficult to build your desired application on any of these.
This is where DecCom comes in. With just a few lines of code you too can build a complex distributed application ready for a production environment. The modular nature of the protocols means that you can modify and add functionality without needing to rewrite your entire codebase. DecCom comes prepackaged with several common protocols which take care of the boring stuff for you - processing large messages, reliable communication, peer discovery, security, etc.
But why "DecCom"? - DecCom is short for Decentralised Communication. There isn't much more to it.
DecCom's philosophy
Many protocol architectures have a very rigid structure - one layer binds to all ports of a lower layer and provides some ports to the layer above it. DecCom violates this strucutre by allowing for any layer to connect to any set of bindings of layers under it. This may sometimes result in very ugly looking diagrams such as the one below.
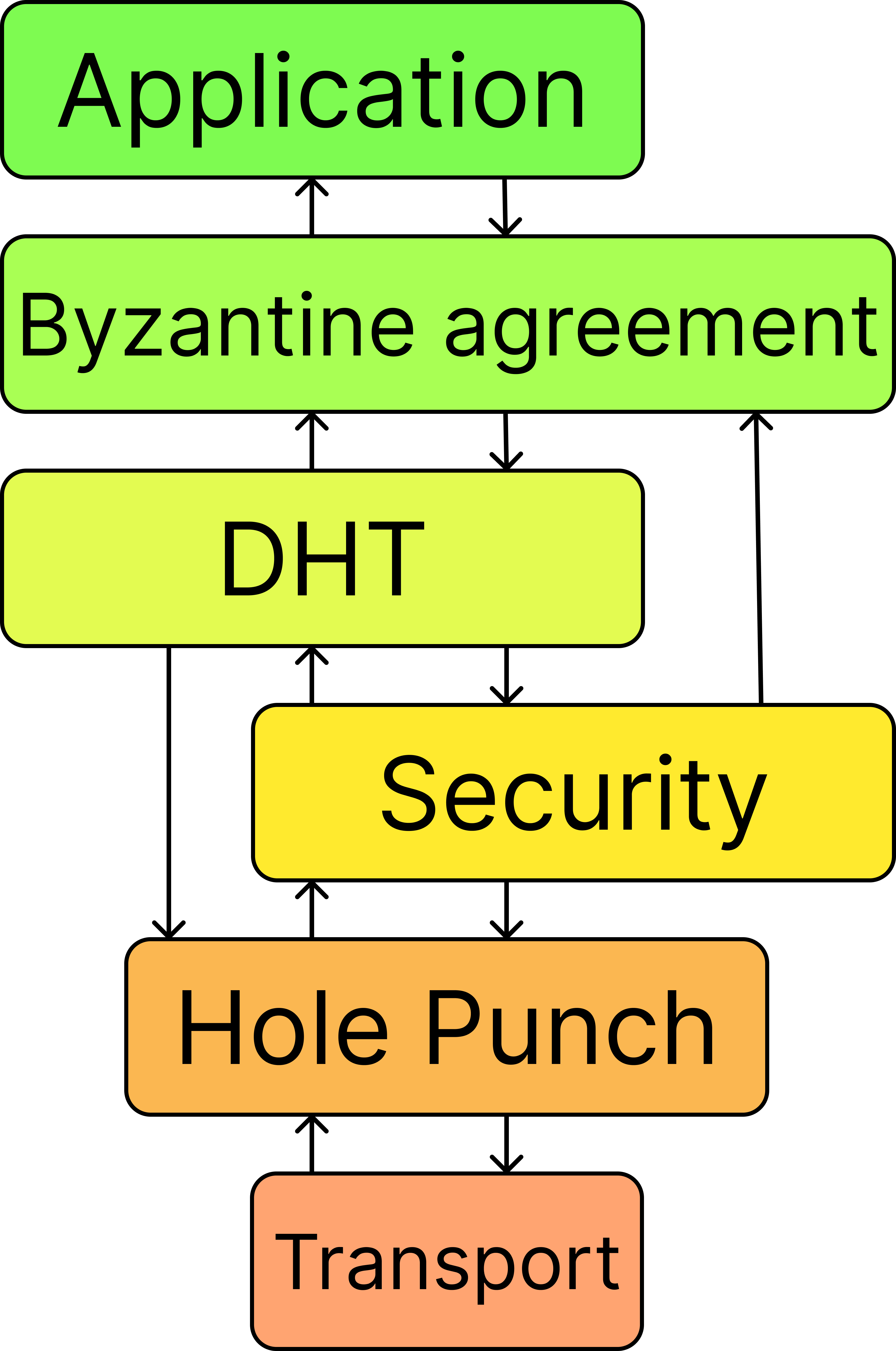
DecCom works with two types of bindings - bindto and bindfrom. Bindto refers to methods a protocol calls from a lower protocol. For example, in the TCP/IP protocol stack, an application would call a "send" method to send to some other IP their message. Bindfrom are methods a lower protocol can call in an upper protocol. In the TCP/IP analogy an application would have a receive method which the lower layer would call when the entire message has been received. Thus bindto goes down, bindfrom goes up the stack. Typically your application should stand at the top.
Wit
Identity
Within DecCom each node has an identifier and a public identity. The identifier is a SHA256 has of their public identity. Their public identity can be a public key (currently we support eliptic curve algorithms on the Ed25519 curve) or strings of arbitrary length. Public key identities are used in security layers for encrypting or signing messages.
Discovery
Discovery can be performed with any of the available methods (currently a Kademlia DHT or a Gossip protocol). It is important to note that depending on the nodes you choose to connect to initially you can have many different peer networks built on DecCom, which do not communicate with each other. Unlike applications built on top of IPFS which use the IPFS network at all times, with DecCom you can create your own private group without ever contacting any of the publicly available ones.
Protocols
DecCom currently has the following protocols implemented:
- UDP transport
- TCP transport
- UDP hole punching
- TCP hole punching
- Reliable UDP
- Noise protocol which establishes a common secret between two nodes
- Kademlia DHT for discovery
- Gossip for discovery
- Delay protocol for testing purposes as one might want to add artificial delay between nodes